Embedded Systems and Security
| Lecturer (assistant) | |
|---|---|
| Number | 0000004160 |
| Type | lecture |
| Duration | 2 SWS |
| Term | Wintersemester 2024/25 |
| Language of instruction | English |
| Position within curricula | See TUMonline |
| Dates | See TUMonline |
- 15.10.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 17.10.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 22.10.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 24.10.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 29.10.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 31.10.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 05.11.2024 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 05.11.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 07.11.2024 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 07.11.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 08.11.2024 08:30-11:30 -1947, Studentenarb. m. DV
- 12.11.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 14.11.2024 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 14.11.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 15.11.2024 08:30-11:30 -1947, Studentenarb. m. DV
- 18.11.2024 13:00-15:00 -1947, Studentenarb. m. DV
- 19.11.2024 09:00-11:00 -1947, Studentenarb. m. DV
- 19.11.2024 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 19.11.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 21.11.2024 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 21.11.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 22.11.2024 08:30-11:30 -1947, Studentenarb. m. DV
- 26.11.2024 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 26.11.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 28.11.2024 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 28.11.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 29.11.2024 08:30-11:30 -1947, Studentenarb. m. DV
- 03.12.2024 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 03.12.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 10.12.2024 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 10.12.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 12.12.2024 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 12.12.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 13.12.2024 08:30-11:30 -1947, Studentenarb. m. DV
- 17.12.2024 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 17.12.2024 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 19.12.2024 08:30-10:00 Z921, Studentenarbeitsraum m. DV
- 19.12.2024 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 19.12.2024 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 20.12.2024 08:30-11:30 -1947, Studentenarb. m. DV
- 07.01.2025 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 07.01.2025 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 09.01.2025 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 09.01.2025 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 10.01.2025 08:30-11:30 -1947, Studentenarb. m. DV
- 14.01.2025 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 14.01.2025 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 16.01.2025 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 16.01.2025 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 17.01.2025 08:30-11:30 -1947, Studentenarb. m. DV
- 21.01.2025 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 21.01.2025 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 23.01.2025 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 23.01.2025 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 24.01.2025 08:30-11:30 -1947, Studentenarb. m. DV
- 28.01.2025 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 28.01.2025 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 30.01.2025 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 30.01.2025 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 31.01.2025 08:30-11:30 -1947, Studentenarb. m. DV
- 04.02.2025 10:00-13:00 Z921, Studentenarbeitsraum m. DV
- 04.02.2025 16:45-18:15 N 1189, Hans-Piloty-Hörsaal
- 06.02.2025 10:00-15:00 Z921, Studentenarbeitsraum m. DV
- 06.02.2025 16:45-18:15 N 1179, Wilhelm-Nusselt-Hörsaal
- 07.02.2025 08:30-11:30 -1947, Studentenarb. m. DV
- 09.04.2025 10:00-11:30 N 1070 ZG, Lothar-Rohde-Hörsaal , Exam review with previous registration in the moodle course.
Admission information
Objectives
The students shall be able to design a secure embedded system. In particular, to implement given tasks on an embedded system and to assess and choose appropriate measures to secure an embedded system. The former includes being able to
- Use toolchains for embedded development
- Discuss memory organisation
- Classify types of on-chip memory
- Recall the boot process of a uC
- Describe and use memory mapped I/O
- List common peripherals and explain their purpose
- Explain and use interrupts
- Compare and use methods for embedded debugging
while the latter encompasses the ability to
- List security objectives
- Exemplify typical vulnerabilities
- Apply some common attacks
- Choose appropriate countermeasures
- Use cryptography
- Illustrate methods for separation
- Explain and use MMUs/MPUs
- Explain side channels
- Demonstrate the concept of trusted computing
- Use toolchains for embedded development
- Discuss memory organisation
- Classify types of on-chip memory
- Recall the boot process of a uC
- Describe and use memory mapped I/O
- List common peripherals and explain their purpose
- Explain and use interrupts
- Compare and use methods for embedded debugging
while the latter encompasses the ability to
- List security objectives
- Exemplify typical vulnerabilities
- Apply some common attacks
- Choose appropriate countermeasures
- Use cryptography
- Illustrate methods for separation
- Explain and use MMUs/MPUs
- Explain side channels
- Demonstrate the concept of trusted computing
Description
To enable students to implement given tasks on an embedded system, the course will deal with:
- Introduction to microcontrollers, differences to desktop computers
- Memory in embedded systems and its usage by C compilers
- Typical peripherals and their usage
- Interrupts and exceptions
- Embedded debugging
The ability to assess and choose appropriate measures to secure embedded systems motivates:
- Short introduction to security objective and cryptographic operations
- Typical vulnerabilities in embedded systems
- Common attacks and countermeasures
- A note on side-channels
- Concepts of separation and trusted computing
- Introduction to microcontrollers, differences to desktop computers
- Memory in embedded systems and its usage by C compilers
- Typical peripherals and their usage
- Interrupts and exceptions
- Embedded debugging
The ability to assess and choose appropriate measures to secure embedded systems motivates:
- Short introduction to security objective and cryptographic operations
- Typical vulnerabilities in embedded systems
- Common attacks and countermeasures
- A note on side-channels
- Concepts of separation and trusted computing
Prerequisites
C programming
Basic knowledge in computer architectures
Basic knowledge in computer architectures
Teaching and learning methods
Knowledge will be taught using slides and notes on the blackboard. Learning by students is supported within the exercises through interactive problem discussion, group work and live programming. Programming exercises during the semester give students the opportunity to train and show their skills on real hardware.
Examination
The above mentioned abilities of discussing, classifying, recalling, describing, listing, explaining, comparing, exemplifying, choosing, illustrating, and demonstrating will be assessed by answering open questions, analyzing code examples and calculating problems in a written exam making up 80% of the final grade. The abilities of using and applying are assessed through programming exercises during the course, which make up the remaining 20% of the final grade.
Recommended literature
The definitive guide to ARM Cortex-M3 and Cortex-M4 processors
Joseph Yiu
Understanding Cryptography
Christoph Paar, Jan Pelzl
Accompanied lecture slides: http://www.crypto-textbook.com
Handbook of Applied Cryptography
Alfred J. Menezes, Paul C. van Oorschot, Scott A. Vanstone
Download from: http://www.cacr.math.uwaterloo.ca/hac/
Security Engineering
Ross Anderson
Download from: https://www.cl.cam.ac.uk/~rja14/book.html
Joseph Yiu
Understanding Cryptography
Christoph Paar, Jan Pelzl
Accompanied lecture slides: http://www.crypto-textbook.com
Handbook of Applied Cryptography
Alfred J. Menezes, Paul C. van Oorschot, Scott A. Vanstone
Download from: http://www.cacr.math.uwaterloo.ca/hac/
Security Engineering
Ross Anderson
Download from: https://www.cl.cam.ac.uk/~rja14/book.html
Links
Important and additional Information
An additional lab is part of this module.
Offered in winter and summer semester.
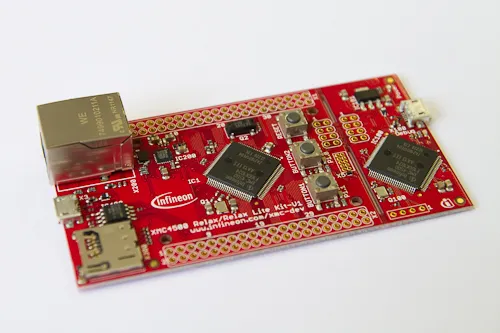
Programming exercises on an embedded system by Infineon will give the opportunity to apply the knowledge acquired in the lectures.
Moodle
Slides will be uploaded to the lecture's Moodle Course after each session.
Language
English (winter semester), German (summer semester)
Marble Run
In the Embedded Systems and Security exercise, the students program a remote control for the marble run in the video on their Infineon XMC4500 Relax Lite board. The marble run ist started in case of a successfull authentication.
As an alternative, the marble run can be started by breaking a 16 bit mini RSA encryption.
It can be accessed unter http://10.152.249.7/ (only from inside the TUM network)