SmartCard Lab
| Lecturer (assistant) | |
|---|---|
| Number | 0000000338 |
| Type | research lab training |
| Duration | 4 SWS |
| Term | Sommersemester 2026 |
| Language of instruction | English |
| Position within curricula | See TUMonline |
| Dates | See TUMonline |
- 21.04.2026 13:15-14:45 N1005ZG, Seminarraum
- 28.04.2026 13:15-14:45 N1005ZG, Seminarraum
Lab Contents
Introduction
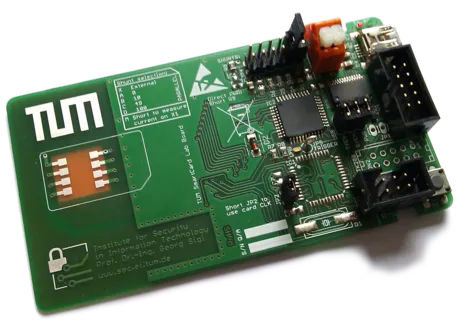
In this lab, you will work in teams of two to explore the security of our SiglTV pay-TV system. As the title suggests, the focus lies on the client side - specifically, the smartcard. Unlike commercial smartcards based on closed-off ASICs, our platform gives you full access to every aspect of the system. Each team will work with our custom-built smartcard based on an ARM Cortex microcontroller.
Throughout the lab, you and your teammate will tackle a series of challenges and compete with your peers.
Lab Challenges
Once you have hold of your smart card, there is only one catch - it’s completely blank. Luckily, your team also receives a reference card containing a valid SiglTV key. This reference card is locked, its decryption master key embedded in the firmware. Taking the role of an adversary, your task is to extract this secret and clone the card.
To achieve this, the first part of the lab focuses on developing a differential power analysis (DPA) attack, exploiting the data-dependent power consumption of CMOS circuits. Once you successfully recover the key, you will implement your own smartcard software stack, the smartcard OS. This includes understanding and implementing the AES cipher, working with the ISO 7816 communication protocol, and ultimately demonstrating your cloned card by decrypting the video stream.
In the second half of the lab, you switch perspectives – from attacker to developer. You will learn how to protect your own implementation against side-channel attacks through a variety of countermeasures. These differ in complexity, performance cost, resource requirements and gained side-channel resistance. Thus, you learn to assess the trade-offs between complexity and security by evaluating the effectiveness of your own side channel-hardened implementations.
To put your implementations to the test, all teams will compete by attacking each other’s implementations. The lab ends with a short presentation of your results and a brief written report.
Prerequisites
Proficiency in C and some experience with microcontrollers are recommended. The introductory sessions will help getting you started and guide you through the hardware platform and show debugging techniques.
Having done the following courses is particularily helpful:
- Introduction into Cryptography
- Secure Implementation of Cryptographic Algorithms
- C/C++ Lab
- Embedded Systems and Security
Teaching and learning methods
The lab combines theoretical lectures with weekly hands-on sessions supported by a tutor. Apart from a few mandatory lectures, you are free to manage your own schedule. Challenges are released every two weeks, providing you some structure and helping you maintain steady progress throughout the course. The number of participants for our lab is predominantly limited by the amount of hardware kits we have available. As of now, each semester a maximum of 25 students can attend.
If you have any questions, please contact tim.music@tum.de